How to get all your corporate “Ops” teams working together, with cybersecurity correctness as a guiding light.
You may also like
With social engineering becoming the leading cause of cyberattacks, it is crucial for businesses to learn how to protect themselves against these […]
The dark web is a part of the internet that is not indexed by search engines like Google. The dark web is […]
Another month, another patch for in-the-wild iPhone malware (and a whole lot more). Read More
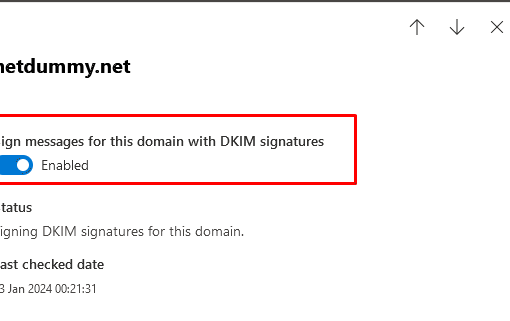
Anti-SPAM implementation covers filtering and blocking incoming spam on receiving and verifying the sender’s allowed hosts thus preventing the likelihood of your […]